
Career Training Paths
Career Training Paths
Suggested career path only, courses can be taken independently, and the order is not fixed.
CPENT TRACK

This track is designed to take you from ground zero all the way through a Licensed Penetration Tester!
You will learn to master an ethical hacking methodology that can be used in a penetration testing or ethical hacking situation. You walk out the door with ethical hacking skills that are highly in demand, as well as the globally recognized Certified Ethical Hacker certification!
In the CPENT course you will encounter cyber ranges built at enterprise level architecture defenses in an to defeat and challenges to overcome. This is not your typical FLAT network! As the challenge levels increase you will encounter the top defenses of today and learn the latest evasion techniques. The format you will use has been used to train thousands of penetration testers globally, it is proven and effective!
For more information:
About any course or track Contact us or to save big, JOIN THE CLUB!
INCIDENT HANDLING & RESPONSE TRACK
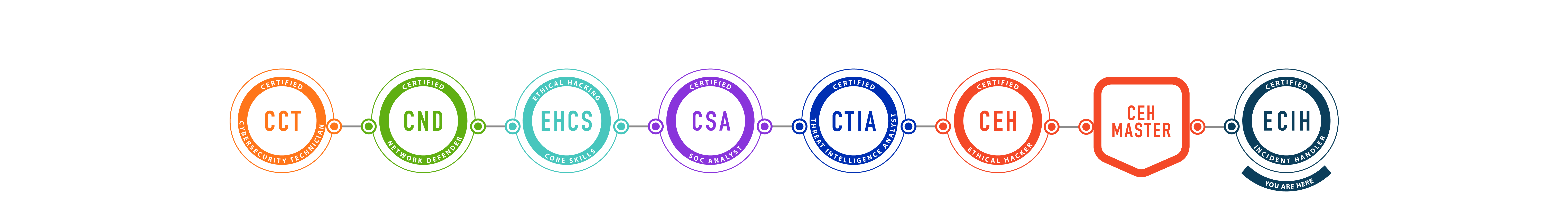
This track is designed to teach you the skills you will need to become a professional Incident Responder!
Cybersecurity Professionals who are interested in pursuing incident handling and response as a career require comprehensive training on Incident Handling and Response (IH&R) concepts as well as real-world scenarios. To help you master IH&R, we have built a track that bundles multiple certification courses to create the most comprehensive IH&R program on the market.
This track begins with the Certified Network Defender and the Ethical Hacker Core Skills programs where you will learn to examine network traffic at the binary level, master TCP/IP protocol, and introduce you to vulnerability assessments and hacking methodology.
Once you have a solid foundation, you will be ready to move into IH&R. The Certified SOC Analyst and Certified Threat Intelligence courses cover the technologies and processes in a SOC as well as the typical Security Incident and Event Management (SIEM) alert triaging process. A unique addition to EC-Council’s IH&R track is the Certified Ethical Hacker (CEH) course, which will teach you the threat hunting skills that are so important to the role.
The capstone to this track is Certified Incident Handler which will teach you best practices to detect, validate, contain, and eradicate security incidents.
For more information:
About any course or track Contact us or to save big, JOIN THE CLUB!
FORENSICS TRACK

This track is designed to teach you the skills you will need to become a professional Computer Forensics Investigator in one year!
This track begins with the Certified Network Defender and the Ethical Hacker Core Skills programs where you will learn to examine network traffic at the binary level, master TCP/IP protocol, and introduce you to vulnerability assessments and hacking methodology.
Once you have a solid foundation, you will be ready to move into ethical hacking and threat hunting with the Certified Ethical Hacker (CEH) course. Learning how hackers break into networks is key to incident handling and response. After mastering the 5 Phases of Ethical Hacking, you will be ready to learn how to detect, validate, contain, and eradicate security incidents.
The capstone of this track is the Computer Hacking Forensic Investigator (CHFI) course, which covers major forensic investigation scenarios and hands-on experience with various forensic investigation techniques and standard forensic tools to successfully carry out a computer forensic investigation. CHFI presents a methodological approach to computer forensics including searching and seizing, chain-of-custody, acquisition, preservation, analysis, and reporting of digital evidence.
For more information:
About any course or track Contact us or to save big, JOIN THE CLUB!

